5 Key Features of the Most Popular Control Panels for Hosting and Development
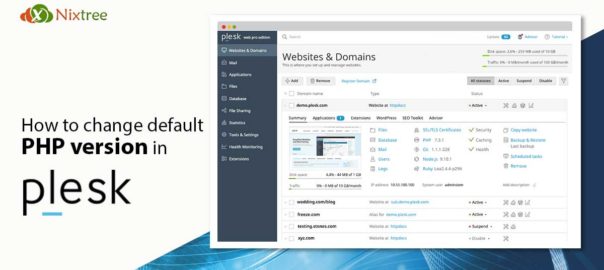
Why Use a Control Panel? Picking the right web hosting control panel can make or break your workflow. Whether you are managing sites, databases, or boosting security and automation, the right panel saves time and effort.Read More…